
by John Helmer, Moscow
@bears_with [1]
A grand jury of steelworkers and coalminers in western Pennsylvania has voted to charge six Russian Army officers with several criminal offences, including defence against two enemy states at war on Russia’s borders, Ukraine and Georgia; the UK’s chemical warfare laboratory at Porton Down; and the Organisation for the Prohibition of Chemical Weapons (OPCW) in The Netherlands.
According to the 50-page indictment by a local US attorney, the Russian soldiers were engaged in a “conspiracy to deploy destructive malware and take other disruptive actions for the strategic benefit of Russia”.
Between April 5 and 6, 2018, the soldiers sent emails pretending to be a journalist from a German national weekly newspaper and a British journalist. The emails were sent to official addresses of the Defence Science & Technology Laboratory (DSTL) [2] at Porton Down in England, and to the OPCW in The Netherlands. Regarding the poisoning incidents in Salisbury of March 4, 2018, involving Sergei and Yulia Skripal, the “Conspirators purported to have information to share regarding the poisoning”.
No evidence has been presented of what information they, or the Russian military intelligence agency GRU at which the six officers worked, had about the Skripal case because their emails were ignored. Malware alleged to be attached to the emails appears to have caused no damage to the targeted computers, nor allowed effective espionage inside the DSTL and OPCW files.
The attempts to communicate with Porton Down and the OPCW have been charged to be the US criminal offences of wire fraud, damage to computers, identity theft, and abetting a scheme of spearphishing – breaking into the computers of Porton Down and OPCW when those organisations were accusing the Russian Army of an attempted assassination by the chemical agent they called Novichok.
The indictment, released on Monday in a blitz of the US and UK media, is the first to make Russian military operations outside the US a criminal offence inside the US. Four of the accused soldiers are accused of having “developed and deployed destructive malware against victim entities around the world, including in the Western District of Pennsylvania”.
Read the full indictment here [3].
Source: https://www.justice.gov/ [3]
The alleged “cyber-enabled malicious actions aimed at supporting broader Russian government efforts – regardless of the consequences to innocent parties and critical infrastructure worldwide – to undermine, retaliate against, or otherwise destabilise: (1) Ukraine; (2) the country of Georgia; (3) France’s elections; (4) efforts to hold Russia accountable for its use of a weapons-grade nerve agent on foreign [British] soil; and (5) the 2018 Winter Olyympics after a Russian government-sponsored doping effort led to Russian athletes being unable to participate under the Russian flag”.
The term “retaliate against” implies that the Russian military operations were in response to prior attacks. However, culpability is assumed in the Skripal poisoning case, and in the campaigns to ban Russian participation in international sports. For the book on the Skripal affair, click [4]. For more on the politics of the anti-doping campaign, read this [5].
The only domestic US case evidence alleged in the indictment claims the Russians launched cyber attacks on a single day, June 27, 2017, against a Pennsylvania health care provider, Heritage Valley Health System; the FedEx Corporation; and Merck & Co., the US pharmaceutical corporation. The damage required a reported $2 million in repairs at Heritage Valley; $400 million at FedEx; $500 million at Merck.
At the time, US press reports indicated [6]the cyber attack was a global one, and that among the targets there was Rosneft, the Russian state oil company. A civil liability lawsuit attempted in the same federal district court in West Pennsylvania by Heritage Valley was dismissed for lack of evidence in August [7]of this year.
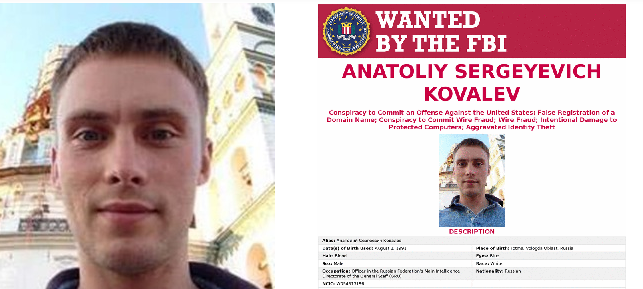
Monday’s indictment also accuses one of the GRU officers, Anatoly Kovalev, of engaging “in spearphishing campaigns for apparent profit, including campaigns targeting large Russian real estate companies, auto dealers, and cryptocurrency miners, including cryptocurrency exchanges located outside of Russia.” No evidence for this allegation has been presented.
Kovalev has also been named [8]in the indictment of July 2018 by Special Counsel Robert Mueller for involvement in US presidential election hacking attempts. The FBI claims [9]Kovalev, a 29-year old native of Vologda, “should be considered armed and dangerous.”
Spearphishing is not defined in the indictment. Kaspersky [10], the Russian internet security company, defines it as“an email or electronic communications scam targeted towards a specific individual, organization or business. Although often intended to steal data for malicious purposes, cybercriminals may also intend to install malware on a targeted user’s computer.” When conducted as part of military operations against hostile forces employing similar weapons and devices, the concept of criminality ceases to apply across the front between the forces; the laws of war take precedence.
The indictment accuses the GRU officers of conducting “three related spearphishing campaigns that targetd the OPCW and UK agencies involved in the investigation of the poisoning”. DSTL at Porton Down is identified as a Ministry of Defence installation. “On or about April 3, 2018, the DSTL announced” – according to the indictment – “that it had identified the poison used against Skripal and others as a military-grade ‘Novichok’ nerve agent”. In point of fact, the only statement [11]from DSTL at the time was carefully qualified so as to rule out the identification of the Russian military as the nerve agent’s manufacturer or source.
Two days after this, on April 5, 2018, Kovalev is now charged as having sent spearphishing emails to DSTL “with malware attached”. No penetration, hacking, or damage at Porton Down’s computers is alleged now, nor the loss of sensitive classified information. A similar GRU operation against the OPCW’s computers also failed.
The OPCW had tested the Skripals in Salisbury Hospital two weeks earlier and was preparing to issue its report of April 12 [12]. Direct Russian spy operations were also under way at the time at the OPCW headquarters in The Hague, and at one of its associated testing laboratories in Spiez [13], Switzerland. The intelligence work resulted in Russian government announcements that the British and OPCW testing had failed to identify a Russian source for the nerve agent identified in the Skripal blood samples.

The author of the indictment and of the grand jury investigation leading up to it is Scott Brady (right), an appointee of the Trump Administration in September 2017. His term runs out next year. Brady describes [14] himself as coming from “a small, blue-collar, steel town in Mercer County, where he learned the value of hard work and the importance of family and public service. Scott worked at an iron foundry to pay his way through Harvard, and upon graduation, worked for faith-based relief and development organizations for seven years, including four in Europe, the Middle East and Central Asia, focusing on post-conflict emergency relief work with refugees.”